Have a music player app on your Android phone? It may be secretly running malware. – 11/16/17
Yes, it has happened again, apps have been found in Google Play loaded with malware. Google has removed 144 different music playing apps from Google Play that contain a new form of malware called Grabos. What makes this malware so devious is it monitors your phone activity and switches its function based on whether you are using the infected app or not. So, when you are paying attention the infected app acts as advertised, letting you download music for free. When you aren’t using the infected app, it sends information about your device, its specs, its location and the apps that are installed on it to the hacker’s server. This information is then used to create targeted notifications that prompt you to download and install additional malware loaded apps which are then opened without your consent.
To make sure as many people as possible are infected, the infected app constantly prompts you to rate it and offers you faster download speeds if you share it with friends.
Because of the prompts to rate these infected apps and their covert nature, many of them have a very high rating on Google Play. The most popular one, with over one million downloads, is called Aristotle Music Audio Player 2017. For a complete list of infected apps, check out McAfee’s blog post.
If one of these is on your phone, uninstall it and then check to make sure all the apps installed on your phone are apps that you installed and were not installed by the malware. It would also be a good idea to change the passwords on all your accounts that you can access from your phone.
Although these apps have been removed from Google Play, they can still be found and downloaded from other locations on the Internet. Reduce your risk, only download apps from reputable sources with good reviews.
Criminals could hack your device through Bluetooth – 9/14/2017
Researchers have discovered a vulnerability in Bluetooth enabled devices that would allow an attacker to take control of them with no action on the part of the user. The majority of manufacturers have issued updates to patch this vulnerability. As Bluetooth is a fairly complicated protocol, experts warn that there may be more vulnerabilities not yet discovered. To protect yourself, make sure you:
- Keep your device updated.
- Turn off Bluetooth when not using it
AirDrop allows strangers to send you files and photos
There is a lovely iOS feature called AirDrop which allows you to sent files to anyone within Bluetooth range anonymously. It has facilitated the rather disturbing practice of bluejacking, sending pics of your privates to random strangers in order enjoy the look of shock on their faces. By default this feature is enabled so you can receive files from anyone on your contact list. However some people have inadvertently changed the settings so they can receive files from anyone.
To prevent such unpleasantness, it is recommended that you disable your AirDrop unless you are using it. To turn AirDrop off:
- Swipe up to view the Control Center.
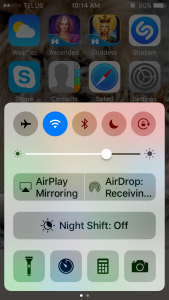
- Select AirDrop Receiving.
- Select Receiving Off.

Android banking malware targets hundreds of apps on Google Play – 04/18/17
It has happened again. Funny Videos 2017 is just one of hundreds of legitimate apps on Google play have been infected with malware. This latest version of malware interacts with the user’s bank and credit card apps, placing a fake login page over the official one. The fake login page collects the user’s login credentials and gives the cyber criminals full access to the user’s bank account or credit card.
Google has removed the infected apps from Google Play. Unfortunately that doesn’t help the users who fell victim. How do you reduce the possibility of being a victim of an infected app? Before you download an app:
- Read user reviews
- Install anti-virus software on your phone
In addition, don’t download apps that ask for unusual permissions (ie. asking for the ability to change settings). Once an app is downloaded, if your phone start behaving unexpectedly uninstall it immediately. If the behavior continues, perform a factory reset on your phone.
What you need to know about crossing the border – 02/10/17
After a Canadian woman was required to surrender her cell phone to US border guards last week and then denied entry, people are wondering what they can do to protect their privacy. Unfortunately, not a whole lot. When crossing the border, you are entering a foreign country and their laws take precedence. They can scan your phone, laptop, tablet or any other device for content as they wish. Any information they find can be used against you. Any sensitive data that is stored can be exposed.
The best way to protect your privacy and that of Mount Royal is to not bring a device with you. Leave your smartphone, tablet or laptop at home. This is especially true if you are traveling to countries with less than honest border guards who are known hold on to your device until you pay a fine. If you are traveling for business and require portable devices:
- Ensure that portable devices are wiped clean of anything you want to remain private. This includes removing social media apps and deleting browser, email and text message history.
- Store data you need access to on Google drive or leave it on your workstation and then use SRAS to access it from your hotel.
- Make sure you remove your Mount Royal email account from your phone and devices and log out of Google.
Basically you want to turn your smartphone into a phone. It takes calls and that’s it. Theoretically they could ask you to login to your email anyway, however the odds are they are not going to bother.
If you need specific legal advice concerning crossing the border as a Mount Royal University employee, contact Legal Services.
One last piece of advice, be nice to the border guards. Declaring that you have rights as a Canadian citizen will only aggravate them. You are attempting to enter their country, our privacy laws do not apply.
Banking App Locks your Phone While your Account is Emptied – 12/2/16
Here is the latest malware scam. Cyber criminals are sending out phishing emails that appear to come from your bank and include a link to download a new banking app on your phone. The email notifies you that for the app to work, you will have to give it administrative privileges. When you download the app, everything works fine. You can make transactions just as you did with your old app. However, after after you have completed several transactions, your phone will not recognize your unlock password. While you are distracted with your locked phone, the criminals are busy emptying your bank accounts using all the information that you entered earlier into their fake app.
Sound scary? It is. How do you protect yourself? Easy, don’t download apps from unsolicited emails. Only download apps from reputable sources such as iTunes, the Google Play Store or vendors/banks legitimate websites. When downloading from a store, make sure you check reviews before you download. Safe apps have millions of downloads and good reviews.
What do you do if you become a victim? Call your bank immediately and do a factory reset on your phone.
Securing your Mobile Devices – 11/03/16
Using Public WiFi Safely – 08/29/16
Keeping your Mobile Device Secure – 08/29/16
Our mobile devices have made our lives easier and more fun. However, because they are mobile it is easy to loose them or for someone to steal them. Also, because they are essentially mini computers, they are also susceptible to malware. Watch the video for some great tips on keeping your mobile device safe.
