How passwords are cracked – 09/18/18
Netflix, Hulu and HBO Go passwords on the dark web – 08/23/18
If you have a Netflix, Hulu or HBO Go account, you should reset your password. Irdeto has reported finding passwords to those services for sale on the dark web. This is an easy fix if you have a unique password for every account. If however you reuse passwords, this news is going to ruin your day. Good luck even remembering all the accounts that you have little own which ones use the same password.
I hate to sound like a broken record, but this is just one more reason to make sure you use unique passwords on all your accounts. This might also be a good time to break down and start using a password manager to keep track of all of them as well.
Using your @mtroyal email for personal stuff? Please don’t. – 07/20/18
On a regular basis, account providers are hacked and their customer data is stolen and put up for sale on the dark web in large data dumps. Usernames and passwords are often included in the information. As over 30% of users reuse passwords and usernames, once a hacker has that information they can access several accounts. As part of our ongoing efforts to keep Mount Royal’s data safe, we subscribe to a service that lets us know if any @mtroyal.ca email addresses appear in these lists. If an account provider gets hacked and a user used an @mtroyal.ca email address as a username, we get notified about the breach. This happens about 3.8 times a month. We then force a password change on the account to ensure it stays secure.
Where things get uncomfortable is when users decide to use their @mtroyal.ca email address for personal accounts. Many account providers who deliver special interest content do not have the best security practices and are often hacked. We really don’t want to know that you belong to the Jelly of the Month Club or you are a member of Poniverse (those are the G-rated ones). Please save us and yourselves the embarrassment. Use your @mtroyal.ca account for business purposes only.
Twitter asking users to change their passwords – 05/04/18
Why is twitter asking all its users to change their passwords? They discovered that login credentials were being stored unmasked in an internal log. This means anyone at the company who opened this log could see users’ passwords and usernames. A HUGE no no. The good news is, they have no evidence that suggests any passwords or account information have been stolen. Now this doesn’t mean that some Twitter systems analyst hasn’t taken down your credentials to use at a later date, it just means they don’t think it has happened.
While this is a huge embarrassment for Twitter, for most of its users it will likely be nothing more than a lesson on the importance of having two step verification enabled. Those lucky ones who reuse passwords will also be reminded why it is better not to as they scramble to remember all the accounts that use the newly exposed password.
Must Read – Help us keep your data safe – 04/17/18
Keeping our digital campus safe is a responsibility shared by the entire MRU community. An important part of that responsibility is for each of us to keep our account passwords secure, private, and not shared with any other person.
Sharing usernames and passwords is never a smart practice, but it’s especially unwise with your MRU account. Your username and password authenticate your identity, proving that you’re you. Many critical University business functions are online these days, and sharing passwords puts all those processes at risk. Whether it’s access to change grades, financial approvals, expense reimbursements, access to staff and student personal information, or simply private emails, your password is how you protect the important work you do from bad outcomes.
Never give your MRU account password to anyone. IT Services will never ask you for it, and neither should anyone else.
If you have a guest that requires a computer for presentations or a meeting, they must bring their own and connect to the “MRVisitor” wifi network. They are not allowed access to admin workstations or private campus networks.
Visiting instructors can log into academic workstations using an SCC account, which allows us to track their activities on our network. The SCC password changes frequently; to get today’s password, please contact the IT Service Desk at itservicedesk@mtroyal.ca, 403.440.6000, or in person at E251.
If you have a situation where you are tempted to share your password, contact the Service Desk and work with them to find a better solution. Together, we can keep our digital resources and online community safe.
Criminals find a way around two step verification in Google – 04/11/18
Two step verification keeps criminals from accessing your account if your password is compromised. It is a great way to add an added level of security to your accounts. However, enterprising criminals have found a way around it.
How did they do it? Is there some back door that they found? Have they created a new brute force hack technique? Nope. They just ask for the verification code. Low tech social engineering strikes again.
Here is how it works. They send you a text that looks like it comes from Google notifying you of a password reset. If you don’t want your password reset, you are instructed to text the word STOP. Once you do, you are asked to text 822 back to be sent a verification code to stop the password reset. Once you receive the verification code, they ask you to text them the code back to confirm that you don’t want the password reset. Pretty clever huh?
Of course what is happening is they are trying to get into your account but can’t because they don’t have the verification code. By playing the stop the password reset game they are hoping to catch you off guard so you just sent them the code.
For the record, no one will ask you if you don’t want to do something with your account. As soon as someone asks you for confirmation to NOT do something, you know the jig is up. This is just another reminder that we have to read our texts and emails carefully and question anything that seems odd. The criminals count on you to react without thinking. Stop them in their tracks, think before you react.
Storing passwords in Chrome and Firefox? It’s just not secure. – 03/21/18
Both Firefox and Chrome allow you to save your passwords directly in the browser. It seems like a handy little feature. However, neither are terribly secure methods for storing passwords.
Chrome doesn’t password protect your stored passwords. All one needs to have access to all your passwords is to access your Google account. This isn’t a problem if you are the only one using a particular device. However if you login to other devices besides your own and forget to log out, you give the next person who logs in access to not just your Google account but to all your passwords as well. This makes it a less than ideal tool for password storage.
Firefox allows you to set a master password to keep your stored passwords safe. However, it uses less than ideal measures to keep the master password from being hacked. This makes saving passwords in Firefox rather an insecure option for your password storage.
What is safe? In truth, no method of password storage is completely safe except for memorization. However, your best bet is still a third party password manager. Regardless of which one you choose, they all give your passwords adequate security. Best of all they generate strong and effective passwords for you so you only have to be creative once.
Passwords are NEVER to be shared – 12/06/17
I was shocked and extremely concerned to read about UK members of Parliament sharing passwords with their staff. How could high ranking members of a government, with a gateway into a network containing super sensitive data be so reckless? Surely no such thing occurs in other organizations? Surely here at Mount Royal University we are much more cautious with our passwords.
I was dismayed to discover that is not the case. Passwords are being shared between professors and graduate students, between managers and admins, between colleagues and between students . Why is this a problem? Just think for a minute of everything that you access with that login information. Do you really want to give someone else that much information about you? Do you really want someone else to be able to access EVERYTHING that you have access to? Your password is the keys to your kingdom. Don’t give it away.
IT Services is very aware that there are many instances where you need to give people access to your email, documents or an application. Fortunately, we have many tools at our disposal to do that without giving them access to everything else as well.
My favorite password sharing excuse is, “I can never remember my passwords, I need my admin to know them so she can remind me when I forget” . KeePass is a password manager that is easy to use and it will store your passwords for you. It is installed on every workstation and it requires you to remember only one password. Still challenged? There are many ways to create a password that is easy to remember but very effective. Contact the IT Security Training Analyst if you are still struggling.
If you are currently sharing your passwords or using someone else’s passwords; please stop, change your password and contact the IT Service Desk to discuss your needs. They will be happy to find a solution for you. Keep your data safe, keep your passwords a secret.
Get notified when your email credentials have been stolen – 09/01/2017
As the majority of account providers use email for usernames, a compromised email can give hackers access to all of your accounts. This is especially true if you tend to use the same password for multiple accounts. Ideally, you should have a unique password for every account so if one account is compromised the rest are safe. You should also be using a password manager to make storage and generation of passwords easy and secure. However, being the realist that I am I know many of you are still using the same password across multiple accounts.
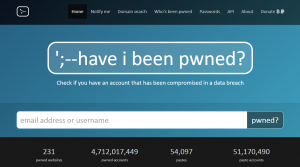
Have I Been Pwned to the rescue!! After Adobe was hacked in 2013 the website Have I Been Pwned was created. The website allows users to enter their email and find out if the associated credentials appear in for sale lists on the Dark Web. This handy little website also lets you sign up for notifications, informing you the minute they discover that your email credentials have been compromised.
Interestingly enough, many hackers don’t actually use the credentials they steal. Instead they sell them to other hackers who use them at their leisure. This practice gives users a chance to change their credentials before any damage is done. Have I Been Pwned was created with this in mind.
You may be thinking…why sign up for this service, won’t I be notified by the account provider when they have a data breach? Unfortunately, account providers haven’t always been the first ones to detect a data breach and they are sometimes reluctant to inform their users that a breach has occurred. For this reason, we strongly recommend that you check out www.haveibeenpwned.com and sign up for notifications. The sooner you are aware that your account has been compromised, the sooner you can take corrective action.
How to Limit the Potential Damage from Stolen Credentials – 05/11/17
Another day, another list of Mount Royal emails that may have been compromised. How? The emails were used as usernames to login to external websites/accounts. These external websites then had their user’s login credentials stolen. This is not a concern if each website has a unique password. However if you reuse the same username and password combinations for multiple websites, once one is compromised they are all compromised.
As it is not a question of if but when one of your websites has their user’s credentials stolen, how do you minimize the damage?
- Avoid using your Mount Royal email to login to external websites whenever possible. Some sites require your work email to access their services. However the majority of sites allow you to enter any email address.
- Create a separate gmail account for logging in to work related websites. New accounts can be created/added from the Google login page. Once a new account has been added, you can view its inbox on a separate tab giving you access to both your accounts at once.
- Use personal emails for personal sites. This will save you from embarrassment. When a site has a Mount Royal email in its list of usernames and it gets hacked, we are notified. We really don’t want to know that you have a Neopets account.
- Use a unique password for every website. Having difficulty coming up with and storing so many passwords? Use a password manager to store and generate passwords.
- Change your passwords regularly. A significant amount of time often passes before theft of login credentials is detected giving criminals lots of time to use them before they are changed. Changing your password makes stolen credentials useless.
