Netflix, Hulu and HBO Go passwords on the dark web – 08/23/18
If you have a Netflix, Hulu or HBO Go account, you should reset your password. Irdeto has reported finding passwords to those services for sale on the dark web. This is an easy fix if you have a unique password for every account. If however you reuse passwords, this news is going to ruin your day. Good luck even remembering all the accounts that you have little own which ones use the same password.
I hate to sound like a broken record, but this is just one more reason to make sure you use unique passwords on all your accounts. This might also be a good time to break down and start using a password manager to keep track of all of them as well.
TeenSafe has leaked data from thousands of account holders – 05/22/18
Researchers have stumbled across two of TeenSafe‘s servers containing databases that list parent emails, their child’s Apple ID email address and password, device names and unique identifiers in plain text. Because the information isn’t encrypted, anyone who gains access to the server can read the information.
Once TeenSafe was notified of the leak, the servers were taken off line. However, if you are a user of TeenSafe, you should change your password and have your child change their Apple ID password. Of course, if you have reused passwords you will also have to change the password for every account that uses the same password. Just another reminder to use a unique password for every account.
ALERT – Mount Royal targeted with fake Sharefile requests – 04/12/18
A college that we communicate with regularly has had one of their email accounts compromised. As a result, several people around campus have received emails with requests to Download Attachments from Sharefile. The emails look like this:

The name of the college and the email sender have been blurred out to protect their privacy.
What makes these emails so devious is that they come from someone that Mount Royal staff have been conversing with recently. This makes it much more challenging to identify them as malicious.
This is a gentle reminder to everyone to contact the email sender when you receive an unexpected email with a link or attachment using a contact number that you have used in the past or have found through Google. Even if you have been speaking with them recently if you aren’t expecting the email, call to confirm its legitimacy. Just because an email looks like it comes from someone you know, doesn’t mean it does.
That is what our brave Mount Royal employee did and as a result prevented a potentially serious cyber security incident. Had they simply clicked on the Download Attachments button and followed the instructions, they would have given the hacker their Docusign credentials. Who knows what that would have led to.
MyFitnessPal Under Armour App has been Breached – 04/03/18

If you have been using MyFitnessPal from Under Armour, change your password immediately. On March 25 Under Armour learned that usernames, email addresses and hashed passwords were taken from about 150 million user accounts.
The good news is the passwords were hashed or scrambled and will need to be decoded before they can be used. The bad new is, the thieves may use phishing emails to acquire your password directly instead of doing the hard work of decoding it. Change your password directly in the app or through their website instead of using a link in an email.
If you use your MyFitnessPal password for other apps or websites, make sure you change those passwords as well.
Travel company hit by data breach – 03/21/18
Did you book travel online between January 1, 2016 and December 22, 2017? If so your payment card information, date of birth, phone number, email address, full name, gender and mailing address may be in the hands of hackers. Orbitz online travel has reported hackers have infiltrated an older version of their booking platform, exposing the data of over 800 000 customers.
As Orbitz is used by other companies such as AMEX to book travel, the breach reaches beyond Orbitz’s direct customers. So how do you know if you have been affected? Orbitz and its business partners will be reaching out to notify you. However, in the meantime keep an eye on your bank statements, credit card balances and credit report. The good news is Orbitz’s current systems have not been affected. For more details, visit their website.
Preventing Identify Theft – 09/12/17
With the news of the Equifax breach consumers are left reeling, not sure what action to take to prevent identity theft. There are tons of articles talking about credit freezes, alerts and monitoring. Most of this information refers to laws and services particular to US citizens. Some are not even available in Canada. As a Canadian, what do you do?
1. Contact Equifax
- Visit the Equifax site for details.
- All impacted customers will be contacted directly. If you have not been contacted, call them at 1-866-699-5712.
2. Set up a credit file alert.
- With a credit file alert, a request for a new credit product or a change in a credit product cannot be approved without confirmation with the consumer who owns the credit. This prevents fraudsters from signing up for new credit cards or loans as well as preventing them from increasing credit limits.
- A credit file alert should be set up with both Equifax Canada and TransUnion Canada. Each provider has different types of alerts and they don’t share information. Contact the companies for details.
- Equifax will be providing free credit monitoring and identify theft protection for 12 months to everyone who is impacted. Equifax will contact you directly with the details.
3. Check your credit report monthly.
- You can get a credit report from Equifax Canada and TransUnion Canada for free.
- Look for signs of fraud.
4. Sign up for credit monitoring.
- Be notified of new debts.
If your identify is stolen or accounts are accessed:
- Contact your local police department and get a police case number.
- Contact all your financial institutions and give them the police case number to hold in your file.
- Call Equifax Canada and TransUnion Canada and have them place the police case number on your credit reports.
- Report the incident to the Canadian Anti-Fraud Centre.
Get notified when your email credentials have been stolen – 09/01/2017
As the majority of account providers use email for usernames, a compromised email can give hackers access to all of your accounts. This is especially true if you tend to use the same password for multiple accounts. Ideally, you should have a unique password for every account so if one account is compromised the rest are safe. You should also be using a password manager to make storage and generation of passwords easy and secure. However, being the realist that I am I know many of you are still using the same password across multiple accounts.
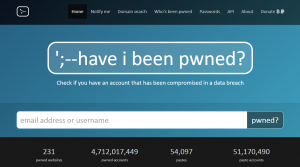
Have I Been Pwned to the rescue!! After Adobe was hacked in 2013 the website Have I Been Pwned was created. The website allows users to enter their email and find out if the associated credentials appear in for sale lists on the Dark Web. This handy little website also lets you sign up for notifications, informing you the minute they discover that your email credentials have been compromised.
Interestingly enough, many hackers don’t actually use the credentials they steal. Instead they sell them to other hackers who use them at their leisure. This practice gives users a chance to change their credentials before any damage is done. Have I Been Pwned was created with this in mind.
You may be thinking…why sign up for this service, won’t I be notified by the account provider when they have a data breach? Unfortunately, account providers haven’t always been the first ones to detect a data breach and they are sometimes reluctant to inform their users that a breach has occurred. For this reason, we strongly recommend that you check out www.haveibeenpwned.com and sign up for notifications. The sooner you are aware that your account has been compromised, the sooner you can take corrective action.
How to Limit the Potential Damage from Stolen Credentials – 05/11/17
Another day, another list of Mount Royal emails that may have been compromised. How? The emails were used as usernames to login to external websites/accounts. These external websites then had their user’s login credentials stolen. This is not a concern if each website has a unique password. However if you reuse the same username and password combinations for multiple websites, once one is compromised they are all compromised.
As it is not a question of if but when one of your websites has their user’s credentials stolen, how do you minimize the damage?
- Avoid using your Mount Royal email to login to external websites whenever possible. Some sites require your work email to access their services. However the majority of sites allow you to enter any email address.
- Create a separate gmail account for logging in to work related websites. New accounts can be created/added from the Google login page. Once a new account has been added, you can view its inbox on a separate tab giving you access to both your accounts at once.
- Use personal emails for personal sites. This will save you from embarrassment. When a site has a Mount Royal email in its list of usernames and it gets hacked, we are notified. We really don’t want to know that you have a Neopets account.
- Use a unique password for every website. Having difficulty coming up with and storing so many passwords? Use a password manager to store and generate passwords.
- Change your passwords regularly. A significant amount of time often passes before theft of login credentials is detected giving criminals lots of time to use them before they are changed. Changing your password makes stolen credentials useless.
Help!! I can’t get into my Gmail account – 03/30/2017
You begin your day like any other, logging into your computer and then logging into your Gmail to check the day’s messages. But this morning is different. For some reason your password isn’t working. You are certain that you are entering the correct password. You have checked to see if Caps Lock is on and still you can’t get in. What do you do?
Your first step is to call the Service Desk. There is a very big possibility that your Gmail account has been compromised. Especially if you use your Gmail username and password combination to login to other accounts.
Once the Service Desk has reset your password and you can get into your account, you need to check your settings. As mentioned in a previous post, once cyber criminals break into your account they like to change its settings so they can regain control of it once you get wise. By checking your account settings, you can make sure your signature hasn’t been changed, that your name appears in the Sent field, that your mail isn’t being forwarded to the criminal and they haven’t given themselves additional access to your account.
Want to decrease the chance that your account will be compromised in the future? Enable two step verification on your account and don’t use your Gmail password for other accounts.
Satan Ransomware Removal Instructions – 01/23/17
Sooo, you have been nailed by the Satan Ransomware bug. What do you do? Well, if the nasty thing is sitting on a Mount Royal workstation, device or laptop call the ITS Service Desk. If it is your home machines or device, no worries because you have followed our terrific advice and have backed up your data regularly…right? If you didn’t quite get around to that all is not lost. Some nice people at PCrisk have a solution for you. More specifically the wonderful Tomas Meskauskas has written an article detailing how to get rid of the awful thing. Do note, that his instructions only apply to the Satan Ransomware bug. If you have another version of ransomware, his procedure will not work. Once you have followed his advice and successfully averted disaster, do remember to perform those regular backups. The next time you get a ransomware infection, there might not be removal instructions for it.
