Authenticator apps, the good, the bad and the ugly 04/03/19
With compromised passwords floating around the dark web like masses of lemmings, two-factor authentication is moving from nice-to-have to a must. Unfortunately, the most commonly used second factor is a SMS text message. Although this method is easy for account providers to implement, it can also be compromised.
Fortunately, more and more account providers are recognizing this and they are integrating with authenticator apps. An authenticator app is a phone app that either generates an authorization code for you or provides the user with a prompt they can respond to. As the phone number is not used to deliver the code, the 2FA cannot be bypassed by a SIM swap.
There are several well known authenticator apps on the market. The top ones are Google Authenticator, Microsoft Authenticator, 1Password, LastPass Authenticator and Authy. All are free to try out. For the most part, they work pretty much the same way. You set them up by either scaning a QR code or entering a key to register your account with the app. When you go to login, the code appears in the app with a count down showing you how long it is valid for. You enter the code and shazam, you are in!
What sets them apart are the added features. Lets start with Google Authenticator. As it is free, simple to use. As it is by Google it is often highly rated by reviewers. However, the devil is in the details and one huge detail is you cannot backup your authenticator keys. This is a big problem if you get a new phone. It is also the reason why it is so poorly rated on the Apple Store. No one wants to spend days re-authenticating dozens of sites. This puts it squarely in the category of ugly.
Next up is Microsoft Authenticator. It works pretty much like the Google one for non Microsoft accounts. However, with Microsoft accounts you can use your phone’s biometrics or PIN to login instead of entering a password. This is a slick feature if you use a lot of Microsoft products and its free. Unlike Google Authenticator you can backup your authorization keys, but you must have a Microsoft account to do it. I put this one in the good category for Microsoft users and in the bad category for everyone else.
On to 1Password. This app is actually a password manager with an authenticator built in. If you are looking for a full feature password solution, this would be your tool. It is free to try, but you have to purchase it once your trial is over. Like the Microsoft app you can backup your keys and it generates authentication codes for its second factor. This one is also rated good.
We finally arrive at my favorite, LastPass Authenticator. The free version functions on its own like the Microsoft and Google products. However, if you purchase the LastPass password manager you can backup your keys plus you get this nice little feature that lets you respond to a prompt instead of entering in a code. Winner, winner chicken dinner!! No more entering codes puts this one at the top of my list. Not only is it a full feature password solution, but it makes securing your accounts way less work.
Lastly, is Authy. This little app is free to use, does the job and you can backup your codes. It is a solid solution that is always highly rated. if you don’t want to pay for an authenticator, this is your app. It definitely falls on the good side.
As determining which app is better for you can largely depend on your personal likes and dislikes I recommend you try them out before you commit long term.
On a final note, although authenticator apps may be more secure they still use your phone for the authentication process. If you lose your phone or forget it, you won’t be able to get into your account. Therefore before you enable any type of phone based two-factor authentication, make sure you can print off backup codes and store them in your wallet or purse. If you lose or forget your phone, you can use the the codes to get into your account. Not all accounts have backup codes, the LastPass password manager is one of them, so do your homework before you enable 2FA.
Why enabling two-factor authentication is more important now than ever – 02/28/19
Two-factor authentication (2FA) and it’s cousin, two-step verification is available on a variety of accounts such as Google, Facebook, LinkedIn, Yahoo, Twitter and Instagram. When it is enabled, after you successfully enter your password on a strange computer you are asked to respond to a prompt or enter a verification code sent to your phone. This ensures that even if your password is compromised, your account will stay secure. That is unless the criminal has your phone as well.
If that is the case, you are having one heck of a day and require support that is outside the scope of this article. I hope your phone is password protected and I wish you good luck. I digress. Back to why enabling 2 FA has become so important.
Last month we saw enormous lists of login credentials popup on the dark web. While previously miscreants had to purchase this valuable information, these large collections of usernames and passwords are now available for free. Aspiring Kevin Mitniks the world over can now try their hand at cybercrime, no upfront credential purchase needed.
As a result we have seen a big jump in credential stuffing attacks. Some of them on home security cameras with terrifying results. Ideally you should have a unique password for each account. However if this particular habit has not yet been entrenched, two-factor authentication will save your bacon
Although registering your email on Have I Been Pwned, will let you know if your password has been compromised, it takes time before a data breach shows up on their radar. With 2FA as soon as you receive a verification code or prompt on your phone, you know someone has stolen your password. This early warning system allows you to change the passwords on your accounts that don’t have 2FA before any damage is done.
Hopefully I have convinced you that two-factor authentication is no longer something that is nice to have, but is essential to securing your data. The next question is, “How do I start using it?”. Thankfully, there is this really great quick reference guide that walks you through the steps on how to enable 2FA on your Mount Royal email account. And yes, I wrote it…that’s why it’s really great. If you have any questions or need some help with the process, please feel free to contact me.
You can also come down to Main Street on March 13, April 10 or May 7. I will be there with my prize wheel. If you talk to me about two-factor authentication, you can spin and win.
What is credential stuffing and why should you care? – 02/14/19
Credential stuffing is where hackers take a list of usernames and passwords and use them to try and login to a site. They use computer programs that allows them to test thousands of login credentials in minutes. If someone is reusing passwords or using common or weak passwords they will have no problem accessing those accounts.
So how do you protect yourself against credential stuffing?
- Use unique passwords for every account. I know it is inconvenient and a pain but it really is the only way to protect yourself.
- Use a password manager. This takes the sting out of my first recommendation. Password managers not only store your passwords, but make generating them and logging in a breeze.
- Register with haveibeenpwned.com. If you register your email with them, they will email you when your email address shows up in a data breach. If you are still reusing passwords, this gives you time to change it. Credentials stolen in data breaches often show up on the dark web for sale before the breached company even knows their user’s data has been compromised.
- Enable multi-factor authentication on every account that has it available. Multi-factor authentication and its cousins two-step verification and two factor authentication requires you to enter an authentication code, respond to a prompt from an authentication app or insert an authentication key when you enter your password.
Updated 03/01/22
How we get notified of an account breach – 11/23/18
Not every hacker makes their money by breaking into accounts and stealing funds or ransoming your data. Some hackers are content to simply break into servers and steal usernames. passwords and other personal information that they then sell on the dark web. It is quite a niche business.
To combat this evil, an enterprising fellow name Troy Hunt created a tool that scans the dark web looking for stolen data that is for sale. You can access this information for free at have i been powned. Simply visit the website and enter your email address. It will tell you if any of your accounts using that email have been breached.
This gives you the opportunity to change your password and username or delete the account. This is an easy process if you don’t reuse passwords. It is a huge headache if you do. What’s even cooler, you can subscribe to an alert service so they will automatically notify you when there is a new account breach. This is so awesome, Mount Royal even subscribes.
We get notified when anyone with an @mtroyal.ca email is involved in a breach. We also get told which account was breached. We are aware that password reuse still happens. By being notified of breaches we can make sure our users change their passwords so hackers cannot use their accounts to gain access to the network.
So if you are using your @mtroyal.ca account to sign up for the adult furry website High Tail Hall, we will know about it. To make matters worse, we have to contact you to let you know about the breach. It gets awkward for everyone.
This is a friendly reminder, only use your @mtroyal.ca email account for business. IT Services thanks you.
Must Read – You are our first line of defense – 11/15/18
As part of our phishing training program, I visit repeat clickers and analyze their business processes to determine why they are having difficulty identifying phishing emails. An interesting trend is appearing. Time after time, I hear people say that they thought IT Services had tools that filtered out all malware so anything that reached their inbox was safe to click.
I am going to set the record straight. There is no anti-virus, anti-malware or other type of software or technology that can identify all malware or malicious links. While IT Services has wonderful tools that help them stop most attacks, they cannot stop everything. Every organization is vulnerable to new strains of malware and hundreds of new strains are developed every day. Whether at work or at home, you cannot rely on anti-virus/anti-malware to protect you 100% of the time.
You are our first line of defense. If you avoid clicking or opening something that you shouldn’t, the odds of being victimized decreases exponentially. Simply by pausing when you are triggered emotionally by an email or when an email contains a link or attachment, you can reduce your chances of a cyber attack by 75%. We can’t do it alone, we need your help. Join us in the fight against cyber crime, stop and think before you click.
Must Read – Iranian Hackers are trying to steal university research – 08/31/18
Iranian hackers are sending out phishing emails that appear to come from within a targeted university. The emails contain a link and urge the recipient to sign in to an internal resource, the favorite being the library system. The link is to a fake login page that records login credentials.
The hackers appear to be trying to steal research data. The campaign is world wide with over 16 universities targeted and over 300 fake websites created. Canadian universities are among the targets.
If you receive an email asking you to login to one of our internal resources, do not click on any links in the email. Instead, access that resource using a bookmark or a link on www.mtroyal.ca. You can also contact the department in charge of that resource and ask them if they sent out an email. Pay special attention to emails asking you to login to the library system.
If you are unsure of the legitimacy of any email, you can forward it to abuse@mtroyal.ca and IT Services will be happy to investigate for you.
Using your @mtroyal email for personal stuff? Please don’t. – 07/20/18
On a regular basis, account providers are hacked and their customer data is stolen and put up for sale on the dark web in large data dumps. Usernames and passwords are often included in the information. As over 30% of users reuse passwords and usernames, once a hacker has that information they can access several accounts. As part of our ongoing efforts to keep Mount Royal’s data safe, we subscribe to a service that lets us know if any @mtroyal.ca email addresses appear in these lists. If an account provider gets hacked and a user used an @mtroyal.ca email address as a username, we get notified about the breach. This happens about 3.8 times a month. We then force a password change on the account to ensure it stays secure.
Where things get uncomfortable is when users decide to use their @mtroyal.ca email address for personal accounts. Many account providers who deliver special interest content do not have the best security practices and are often hacked. We really don’t want to know that you belong to the Jelly of the Month Club or you are a member of Poniverse (those are the G-rated ones). Please save us and yourselves the embarrassment. Use your @mtroyal.ca account for business purposes only.
Some Google Groups are leaking data – 06/05/18
Have you checked the settings on your Google Group lately? By default when you create a group, only group members can post and view messages and people must ask to join the group. However, researchers have discovered that thousands of Google groups have their permissions set to allow the general public to view the group posts. This would not be an issue if the people posting information to the Google Group understood that their posts could be viewed by the public. However, sensitive and private information has been found within these group posts suggesting that they really have no idea.
If you are the owner of a Google Group, please take a moment to check your permissions. To check permissions:
- Open the Google Group.
- In the title bar of the Google Group, click Manage. The left menu changes.
- In the left menu, click Permissions. A list of permissions appears.
- Click to select each permission type and review its settings.
Please note that if you have selected All organization members, to View topics or Post anyone with an @mtroyal.ca email address may do so. This includes students, staff and faculty. If you have selected All members of the group, users must actually join the group to be able to post or view emails/topics.
If you wish to email/post to a Google Group, check the settings of the group to see who can see the messages you send. To check the settings:
- Open the Google Group.
- In the title bar of the Google Group, click About.
- Scroll down to find the Access section. The posting and viewing permissions of the group are listed here.
If you have questions or concerns about setting permissions, please contact Bernadette Pasteris at bpasteris@mtroyal.ca.
Hackers using calendar events to deliver malicious links – 05/23/18
Hackers have discovered a new way to deliver malicious links, through your Google calendar. How? Simply by creating a calendar event and inviting you.
By default when you are invited to a Google calendar event, the event appears in your calendar whether you have responded to an invite or not. The sneaky hackers know that if you receive an email with an invite from someone you don’t recognize, the odds are great that you will simple delete it or ignore it. So, they create an event with a vague description and include a link to the meeting agenda but choose to not email the guests.
What the hackers hope is days or weeks later when you receive a meeting notification or see the event sitting in your calendar, you will think you have forgotten about a meeting and will open up the event and click on the link to view the agenda. I know what you are thinking, I wouldn’t fall for that because I would check the meeting owner’s email. Ideally that is exactly what you would do, however when humans think they have messed up they tend to panic and click.
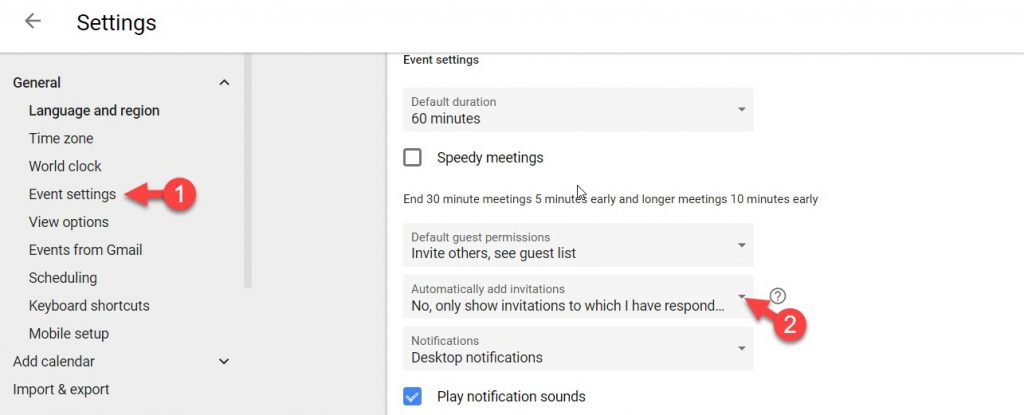
How do you protect yourself from the panic and click? You can change your event settings on your Google calendar. Go to Settings and select Event Settings. In the Automatically add invitations section, select No, only show invitations to which I have responded. This prevents events from being added to your calendar without an email invite so you can’t be ambushed.
Help! I think I have a virus! – 04/24/18
Is your computer acting weird? Is it suddenly working really slowly? Are pop-ups all over your screen? Are folders graying out and can’t be opened? Are files suddenly unavailable or can’t be found? Is your mouse moving on it’s own? Has the text become unreadable? Do you have a virus alert? If you are experiencing any of these, you could have a virus or malware on your computer.
If you think you have malware on your machine, do not turn off your machine, some types of malware load on start up. Do not run a virus scan, some types of malware corrupt anti-virus programs. Do not try to fix the problem yourself. Do not panic, help is available. So what do you do?
- Don’t touch anything. Many types of malware are loaded by clicking anywhere on a pop up window. If you don’t click, you may be able to prevent an infection.
- Disconnect from the Internet. On your workstation, unplug the network cable. On your mobile device, disconnect from wifi.
- Call the IT Service Desk.
Not sure what a network cable looks like? It looks like a phone cable, but comes out of the back of your computer. It can be red, white, black, blue, gray or yellow. Still not sure? Here is a photo for you:

Worried about getting into trouble and you don’t want to call the Service Desk? Please don’t be. IT Services has service in the name for a reason. We are here to help you. We know you are human. We know people make mistakes. We like to get your calls.
