Misspelling a URL can load your computer with malware – 04/24/18
In today’s world of brand recognition, nothing is more important than your domain name. Whether you are Coca-Cola, ESPN or Freds Furniture, you need a web page that people can find just by typing the name of your business. What happens though when a consumer gets the name wrong? On-the-ball businesses buy the domain names for common misspellings of their name and redirect consumers with fat fingers to the correct web site. Those that don’t, leave consumers and their business exposed.
Criminals are buying up the misspelled domain names of popular web sites and loading them with malware. This practice is called typosquatting. It costs businesses millions in sales and untold grief for consumers. In the best case scenario, visiting one of these sites will result in your anti-virus going spastic with pop-ups and alerts. At the worst, malware too new for your anti-virus to recognize will be quietly and efficiently deposited onto your machine. Many of these web sites can only be visited once. A repeat visit results in a 404 web page not found error, making it difficult to shut the site down.
The easiest way to protect yourself from typosquatting is to use bookmarks to visit your favourite sites. When looking for new ones, read and re read the search terms you have entered and then read them again. Don’t let a slip of a finger deliver you into the hands of a hacker.
Cyber Safety Summit 2018 – 04/23/18

The Cyber Safety Summit 2018 will be held on October 2, 2018 at the Lincoln Park room in the Main Building of Mount Royal University’s campus. The summit will include experts speaking on home security, social engineering, fraud protection and how to recover from a cyber attack. In addition we are adding a new topic this year, protecting your privacy. Registration is free.
Spend the whole day with us or just come by for your favourite session. Either way you have the opportunity to hear from the experts themselves how to keep your family and home cyber safe. Come with your questions and concerns, leave armed with the knowledge you need to keep hackers at bay.
Can’t attend the summit? We will be live streaming all sessions. Visit the website to review last year’s program and to sign up for Summit updates.
Mark your calendars now!! See you on October 2, 2018!!
Must Read – Help us keep your data safe – 04/17/18
Keeping our digital campus safe is a responsibility shared by the entire MRU community. An important part of that responsibility is for each of us to keep our account passwords secure, private, and not shared with any other person.
Sharing usernames and passwords is never a smart practice, but it’s especially unwise with your MRU account. Your username and password authenticate your identity, proving that you’re you. Many critical University business functions are online these days, and sharing passwords puts all those processes at risk. Whether it’s access to change grades, financial approvals, expense reimbursements, access to staff and student personal information, or simply private emails, your password is how you protect the important work you do from bad outcomes.
Never give your MRU account password to anyone. IT Services will never ask you for it, and neither should anyone else.
If you have a guest that requires a computer for presentations or a meeting, they must bring their own and connect to the “MRVisitor” wifi network. They are not allowed access to admin workstations or private campus networks.
Visiting instructors can log into academic workstations using an SCC account, which allows us to track their activities on our network. The SCC password changes frequently; to get today’s password, please contact the IT Service Desk at itservicedesk@mtroyal.ca, 403.440.6000, or in person at E251.
If you have a situation where you are tempted to share your password, contact the Service Desk and work with them to find a better solution. Together, we can keep our digital resources and online community safe.
ALERT – Mount Royal staff victimized by phishing email that is a reply to an old thread – 03/26/18
Mount Royal employees are receiving emails from a vendor that are actually replies to a legitimate message. As the message is a reply and it is from someone we do business with, employees have been tricked into opening the attachment more than once putting our network at risk.
How the heck did they manage to reply to a message that the vendor had sent ages ago? Simple, the vendors email account was hacked. Once the hackers had access to the email account all they had to do was scroll through the emails in the sent folder until they found one that mentions an invoice and reply to it. Of course they attached an edited invoice containing a nice little keylogger trojan onto it first.
Those that opened the attachment found a blank document and then contacted the Service Desk to see why. The Service Desk calmly explained all their keystrokes were being recorded by malware they had unintentionally installed and then sent support staff to re-image (wipe clean and re-install) their machines.
Unfortunately this is not the first time that Mount Royal University has been targeted by this type of attack. Late last year another vendor had their email account compromised and multiple Mount Royal staff members received replies to an old meeting invite containing a document that “required their input”. That document contained malware as well and once again we were re-imaging machines.
How do you know when an email from a vendor contains a malicious link or attachment? Truthfully, you don’t. The only red flag on either of these emails was the date of the original message. The email thread was months old and was used in the attack because it contained a subject that would allow an attachment to be added to it without looking odd. However, a recent message could also have been used if it had contained the right content.
So how do you protect yourself from such attacks? You call the vendor when you receive an email with a link or attachment and confirm that they sent the email. You do not reply to the email as if their email account has been compromised, you will be conversing with the hacker. Do not use the contact information found in the email to contact the vendor either. The hacker may have changed the email signature. Use a contact number that you find in a Google search or that you have used before.
Yes, horrors, you have to actually pick up the phone and talk to a person. However, it will practically eliminate the risk of having your machine wiped clean and the operating system re-installed. Not a fun way to spend the morning.
Beware, the locked browser tech support scam is back- 03/13/18
Malwarebytes has discovered an old tech scam that has resurfaced. Hackers are compromising legitimate web sites. When you visit one of these sites, a pop-up appears on your computer telling you that you have a virus and you need to call a 1-800 number. To make it look like there is something wrong with your computer, the browser is locked and doesn’t respond to clicks.
If you call the number, you are asked to download diagnostic software that gives the hackers control of your computer. They then appear to find the virus on your machine and proceed with a hard sell trying to get you to pay to have it removed. In reality there is nothing wrong with your machine.
No software will magically detect issues on your computer without being installed. No browser can detect issues with your computer. Microsoft does not send out alerts to let you know your computer is not working properly or has been compromised. Anytime you receive an alert of any kind with a support phone number, it is a scam.
The good news is, with this particular scam there is nothing wrong with your computer. All you need to do is shut down your browser through the Task Manager and everything goes back to normal. Just remember not to visit the same website again.
To shut down your browser in the Task Manager:
- Press CTRL + ALT + Delete
- Select Start Task Manager
- On the Tasks tab, select your browser
- Click the End Task button.
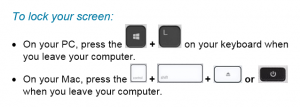
Lock your Screen When you Leave the Scene – 02/07/18
Just a friendly reminder to lock your screen EVERY TIME you leave your workstation unattended. In the time it takes to get a print out or go to the kitchen to throw out garbage, your workstation can be compromised. The hackers need less than a minute to access your workstation and load malware that runs in the background. The malware can be present for months, giving the criminals access to the network and our data without you even being aware that it is there.
It is not enough to say, “Well I usually lock my screen but sometimes I forget.” Usually will not keep our network safe. Always will. Join us in the fight against cyber crime. Be a super hero and lock your screen EVERY TIME!
Payroll related phishing email making the rounds – 02/02/2018

Another day, another phishing attack making the rounds. The latest asks you to confirm your identity by clicking on a link and logging in. These emails often refer to issues with your paycheck or benefits that need to be resolved. Replying to one of these emails and asking for more information results in a very quick and convincing response assuring you everything is on the up and up.
If you ever receive an email asking you to use a link to login to confirm your identify, close the email and login to the site directly using a bookmark or Google search result. If the request is legitimate, you will be able to find it on the official web site. If you cannot find the information and are still not sure of the email’s legitimacy, contact them by phone or email using contact information taken from their official site. If you do determine that the email is a phish, forward it to abuse@mtroyal.ca and then report it as phishing to Google.
As always, if you are in doubt contact the IT Service Desk.
Why you should worry about cryptocurrency mining – 01/26/18
First things first, what is cryptocurrency? Cryptocurrency is digital currency. The most known is Bitcoin, however others are popping up such as Monero. How do they work? Well, I found a nifty little video that tells you the basics. It refers to bitcoin but the premise applies to all cryptocurrencies.
Neat huh? Notice the part where they say it takes lots of computing power and lots of electricity to mine? This is where things get interesting. Criminals have figured out that if they use the computing power of other machines, they can mine more cryptocurrency faster without having to invest in all the computing power or electricity themselves.
Why should you be concerned? More and more malware is mining cryptocurrency. The malware is often hidden on legitimate websites, applications or browser extensions. Why is this a problem? After all it is just using the processing power of my computer, its not actually doing any real harm is it? Well, no and yes. No it isn’t doing anything malicious like encrypting your hard drive or stealing your data. However, it is wearing out your machine and slowing it down. The more clever mining malware waits until you aren’t actually using your machine to mine. This reduces the chance you will notice that it is actually there, but still wears out the processor, eats up bandwidth and increases your electricity bill. Less clever creations, slow your computer down to a noticeable crawl.
Having millions of other peoples computers mining cryptocurrency for you can be quite lucrative. So much so that some websites have turned from using adware to generate revenue to asking users to lend their computing power. This is just fine if the user knows it happens and consents. It is another thing entirely when its done behind the scenes. Finding out your machine is being used for mining after the fact tends to leave you feeling like you need to take a shower. Its just not nice.
So what can you do about it? First of all, if your workstation seems slow contact the Service Desk. If it is your home machine, check the CPU processes to see if you have any spikes in usage. How do you prevent the mining in the first place? The mining software is considered to be malware, so the regular security measures that you take to protect yourself from malware will protect you from crypto mining. Make sure you:
- Use an Ad blocker
- Stay away from shady websites
- Only download software from reputable sites with good reviews
- Beware of browser extensions
New security vulnerabilities found on everything with a computer processor – 01/08/18
What are they?
New vulnerabilities called Meltdown and Spectre have been found in computer processors built after 2009 that allow a program to steal data from your computer system’s memory without your permission or knowledge. It affects everything that has a computer processor including your computer, tablet, phone and IoT (Internet of things such as a smart thermostat).
Why should I be concerned?
These vulnerabilities have the potential to allow hackers to covertly fetch sensitive information such as passwords from system memory allowing access to your online banking, social networking accounts and the like. To make matters worse, the attack can be made via your browser.
How is the problem fixed?
As these vulnerabilities are in the main processing chip on the computer, the ultimate fix will be to change the processor codes, the firmware or the chip itself. However, the problem can be mitigated by modifying how the software interacts with the processor. As a result, software and hardware vendors are currently developing patches for these vulnerabilities.
What is IT Services doing about it?
We are following our standard processes to manage the patches for these vulnerabilities.
What do I have to do?
You do not need to update your workstation, it will be done by the MRU patch management process. Your regular updates include all required patches. If you have a Mount Royal laptop or device and you aren’t sure that it is getting updated, please visit the IT Service Desk.
Install updates for all your personal portable devices and home machines as soon as they become available. Make sure that your browser is updated as well. Please note that not all anti-virus programs are compatible with Microsoft’s latest updates. If your machine has incompatible anti-virus software, the Microsoft updates will not be uploaded and your machine will be left vulnerable. Check your anti-virus program’s website to see if it is compatible.
Make sure you visit official/trusted websites to get your updates or use the update feature from within your software. We do not recommend clicking on links and opening attachments in emails claiming to have a link to the latest updates or patches. Criminals may take this opportunity to send out fake security patch or update emails with malicious links to try and trick you into downloading their malware.
For more details on the vulnerabilities, check out the sources for this article:
- https://security.ias.edu/what-im-doing-about-meltdown-and-spectre
- https://blog.barkly.com/meltdown-spectre-bugs-explained?utm_source=hs_email&utm_medium=email&utm_content=59793819&_hsenc=p2ANqtz-8rqyrd29_vLfOEF9J8ljck2Ww_K7aagIHFIJ6xJd2S0B99cx9imk-7aLq4YL-juWfpdGSfmP80d0yBSK_4WRBT2l-I3A&_hsmi=59793819
- https://krebsonsecurity.com/2018/01/scary-chip-flaws-raise-spectre-of-meltdown/
- http://bgr.com/2018/01/05/meltdown-spectre-fix-windows-patch-anti-virus-updates/
Passwords are NEVER to be shared – 12/06/17
I was shocked and extremely concerned to read about UK members of Parliament sharing passwords with their staff. How could high ranking members of a government, with a gateway into a network containing super sensitive data be so reckless? Surely no such thing occurs in other organizations? Surely here at Mount Royal University we are much more cautious with our passwords.
I was dismayed to discover that is not the case. Passwords are being shared between professors and graduate students, between managers and admins, between colleagues and between students . Why is this a problem? Just think for a minute of everything that you access with that login information. Do you really want to give someone else that much information about you? Do you really want someone else to be able to access EVERYTHING that you have access to? Your password is the keys to your kingdom. Don’t give it away.
IT Services is very aware that there are many instances where you need to give people access to your email, documents or an application. Fortunately, we have many tools at our disposal to do that without giving them access to everything else as well.
My favorite password sharing excuse is, “I can never remember my passwords, I need my admin to know them so she can remind me when I forget” . KeePass is a password manager that is easy to use and it will store your passwords for you. It is installed on every workstation and it requires you to remember only one password. Still challenged? There are many ways to create a password that is easy to remember but very effective. Contact the IT Security Training Analyst if you are still struggling.
If you are currently sharing your passwords or using someone else’s passwords; please stop, change your password and contact the IT Service Desk to discuss your needs. They will be happy to find a solution for you. Keep your data safe, keep your passwords a secret.
