How to check your cybersecurity awareness training status 04/15/21
Reminders are going out for everyone to complete their cybersecurity awareness training. In response people are noticing they have no training assignments and are wondering if they have completed the training or not. These wonderful folks usually completed their training in October.
Unlike Blackboard, the new Security Education Platform doesn’t let you access modules once they are completed. They are removed from your assignment list. However you can still see what training you have completed by looking at your Report Card.
To access your Report Card, click on your name in the upper right hand corner of the platform window and then select My Report Card. It will show you the status of all your assignments.
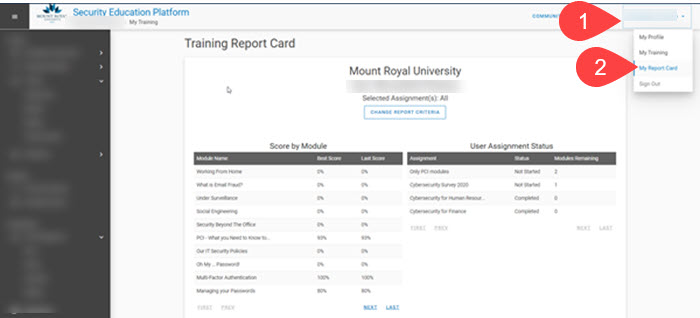
Please note that the name has been blurred out in this screenshot. In addition, you will see the cybersecurity survey in your assignment list. This survey is no longer available. Don’t worry if you didn’t complete it, it was optional.
I hope this helps those of you who can’t remember if you completed your training or not. If you have any other questions about the cybersecurity awareness training, please feel free to continue to contact me.
Let us know what you think of the Be a Superhero branding and earn contest entry codes – 03/01/21

The cybersecurity awareness program at MRU has been around for several years now. Throughout that time we have encouraged the campus community to Be Superheros by practicing cybersafe behavior. While the Be a Superhero branding has worked well for us, we are always looking for ways to make the program more engaging and effective.
We would like your feedback on our branding. Let us know if you still want to Be a Superhero or if it is time to leave our capes behind. You can find the survey here.
Everyone who completes the survey will receive a contest entry code for the Cybersecurity Challenge and a chance to win a $250 Best Buy gift certificate. As this is the last month to collect entry codes, this is a great way to get entries in and move your team forward.
The annual cybersecurity survey – 12/03/20
This week you will have received an email asking you to complete the cybersecurity survey for 2020. This annual survey lets us know what the MRU community has learned over the past year and helps us determine the direction and focus for the year ahead.
This year the survey is being administered through the Security Education Platform. This allows us to more easily analyze the data that we collect. The survey appears in your assignment list. Although it looks like an assessment, it is not. Completion is voluntary. No one sees the individual results except the IT security team and the data will be anonymized for reporting purposes.
We want to know what your cybersecurity habits are as well as what you know. The goal is to determine if the information and tips we are giving you are helping you practice cybersafe behavior or if we need to approach things differently to provide you the support that you need. As a thank you for helping make the program better, everyone who completes the survey by December 21, 2020 receives two contest entry codes into the Cybersecurity Challenge draw for a $250 Best Buy gift certificate.
Cybersecurity Challenge 2019/2020 Winners – 10/29/20
The 2019/2020 Cybersecurity Challenge wrapped up on September 30 last month. A big congratulations to Stephanie Spencer in Continuing Education! She is the winner of the $250.00 gift certificate to Best Buy! Have fun shopping Stephanie.
The winner of the Golden Superhero Award is once again the Facilities Management team. Congratulations team for an outstanding effort! Here is the gang in their COVID glory,

A huge thank you to everyone who participated! It was the best year ever for the Challenge. That said, this year’s Challenge is shaping up to be a close race. For the first time in three year’s, the Facilities Management team is not in first place and the top four teams are running neck and neck. Who will be the winner next year? Tune in on March 31, 2021 and find out!
It’s Cybersecurity Awareness Month! – 10/02/20

Welcome to another Cybersecurity Awareness Month (CSAM)!! Although we can’t meet in person, we do have a full list of activities that you can participate in.
Cybersecurity Challenge 2020/2021
The Challenge is back with several improvements. As before, you earn contest entry codes by participating in cybersecurity activities. Each entry gets you one chance to win a $250 Best Buy gift certificate from Cisco Systems Canada. However the contest now runs from October 1, 2020 to March 31, 2021. This should prevent Challenge fatigue while still ensuring everyone has the opportunity to participate.
The teams have also been updated. They are now only 100 members in size. As all the teams are the same size, the leaderboard will display the actual number of entries rather than percentages. Lastly, the sharing of codes officially became against the rules. If you don’t participate and enter a code, you will be disqualified from the Challenge.
Virtual Treasure Hunt
To replace our Hack the Room activity, we have a virtual treasure hunt. Bluebeard has hidden a chest full of crypto currency. Solve the clues, collect contest entry codes and find the treasure. Everyone who finds the treasure is entered into a draw for a $100 Amazon gift certificate courtesy of WBM Technologies.
The Cybercrime Series
Come join us for tales of cyberhorror. The Cybercrime Series looks at cybernightmares and how to prevent them. We have two scheduled for October.
- Cybersecurity: Are our graduates ready for the new economy? – Angele McAllister
- The Cybersecurity Monster Manual: Stopping things that go “hack” in the night – Michael McDonnell
Double codes for completing training in October
To encourage you to complete your cybersecurity training, we are offering two contest entry codes for completing your training this month.
Our regular activities
Keep an eye out for our regular activities as well. Participating in them earns you contest entry codes for the Challenge. You can subscribe to the newsletter, show off your cybersecurity sticker, join us in the Cybercafe or complete your training.
Workshop and Cybercafe held next week 09/17/20
Next week we have two events being held. September 22, 2020 is the Protecting yourself against cybercrime 2021 workshop from 2:00 pm to 3:30 pm. This is a great opportunity to complete your mandatory training and ask as many questions about cybersecurity as you like.
If you are not able to make the training but still would like to discuss cybersecurity, join us for the Cybercafe on September 24 at 3:00 pm. For 30 minutes you can ask all your burning cybersecurity questions. Our Security Administrator will be joining us, so the questions can get as technical as you like. While you can ask anything you like, I will also be presenting a current news item as a topic of discussion. Check back on September 23 to see what that topic will be.
See you there!
New tool for remote file access coming – 08/12/20
IT Services is proud to announce the imminent arrival of their new remote file access tool, Webfiles. Previously when you clicked on the Remote File Access link in MyMRU, you were directed to SRAS. This allowed you to upload and download files on the Mount Royal network remotely. This tool was used by students, staff and faculty and was linked to our old VPN Pulse Secure.
As of September 7, 2020 Pulse Secure will no longer be supported and SRAS will no longer function. In preparation of this, we have been moving those using Pulse Secure over to our new VPN Global Protect.
Webfiles will replace the SRAS upload and download functionality. Just like SRAS, it is available to students, staff and faculty. If you use the Remote File Access link in MyMRU to access SRAS, sometime before August 24, 2020 the link will be updated to give you access to Webfiles. If you use secure.mtroyal.ca, to access SRAS, please move over to Webfiles before September 7, 2020 to ensure continued access to remote files.
Change is always challenging however Webfiles is much easier to use than SRAS , making this change a welcome one. For details on how to use Webfiles, refer to the user guide Accessing files and folders remotely using Webfiles. For the latest information on remote file access, visit the Working Off-Campus webpage.
New Cybersecurity Awareness Training Platform is Launched 08/12/20
It’s that time of the year again. Last year’s cybersecurity awareness training is being archived and the new training program is being launched. This year we not only have a new program, but we have a brand new tool to deliver it, The Security Education Platform by Proofpoint.
Thanks to this new tool, we are able to mandate cybersecurity awareness training for all employees! While everyone has access to the online training tool, depending on your role you may be able to take a workshop to meet your training requirement. On Monday, August 17 the new training goes live!
If you have any questions about the new training platform, contact me at bpasteris@mtroyal.ca or call me at 403-440-6329.
Power outage on campus this weekend will affect remote desktop users at home – 07/14/20
Employees who are set up to use ‘remote desktop’ will need to save their work and power down their campus PCs from home 8 p.m. on Sat., July 18 for an annual maintenance shutdown. PCs will automatically be turned on the following morning at 8 a.m. Employees who are working on campus will need to power down their PCs and empty fridges of any perishables before leaving work on Friday, July 17.
We are rolling out a new VPN Service – 06/12/20
Currently, people across the University use the Pulse Secure VPN also referred to as SRAS to create a secure encrypted connection between their home machine and their MRU workstation. Unfortunately, budget constraints are requiring us to move to a more cost effective service. The new service is called GlobalProtect. The good news is, it is more powerful and easier to use.
The move from Pulse Secure/SRAS to GlobalProtect is happening in phases. Although everyone on campus who has access to Pulse Secure will also have access to the new service, you aren’t required to move over until you have received a notification with instructions on how to install, configure and use the new service.
The Working Off Campus webpage has everything that you need to know about the move and how to use the new service including user manuals and a list of FAQs. As always, you can contact the Service Desk for support.
We know that working from home is frustrating enough without having to deal with a new service, unfortunately it couldn’t be helped. We apologize for any inconvenience.
