MRU employee checks for email legitimacy and talks to the hacker – 10/17/19
One sure fire way to avoid becoming a victim of a cyberattack is to call the email sender to verify that they in fact sent the email. That is a message that I preach over and over again all over campus. I am happy to report that my message is being heard and acted upon…sort of.
Here is the email that one of our staff received in their inbox.

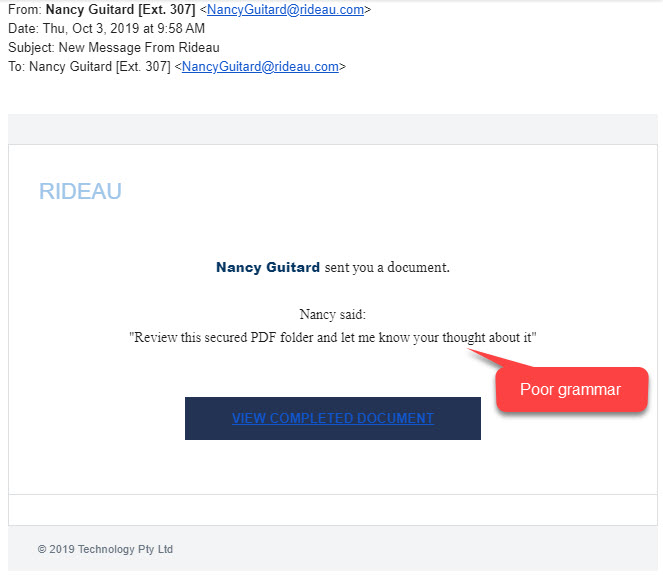
The staff member knows the sender and aside from the poor grammar, the email is spot on. The attachment was indeed a Sharepoint document, so she opened it. However when she found nothing but a greeting link to another document she paused. She knew that email addresses could be spoofed and realized she should confirm the legitimacy of the email. So she sent this email.
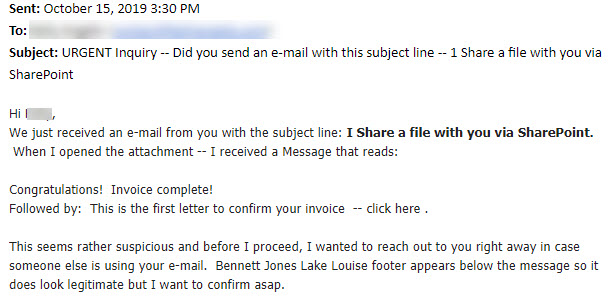
She correctly did not reply to the original email. But created a new one and sent it using an email address in her contact list. This is the reply that she received.

Before she could check the invoice, she received this email.

The sender’s email account had been hacked! It didn’t occur to our staff member that if someone else was using her colleague’s email address, it wouldn’t be her colleague who responded . She gets an A for verifying the legitimacy of the email. But she gets a F for talking to the hacker.
The lesson has been learned. When confirming email legitimacy, use the darn phone. A 30 second phone call can save you from a world of hurt.
Malicious links can hide in legitimate documents – 10/09/19
The tools that cybersecurity professionals use are getting more and more sophisticated. They can now identify a known malicious link or attachment and strip it from the email so it never arrives in your inbox. To get around that limitation, hackers are hiding their malicious links and attachments in legitimate documents. This latest attack is a perfect example of that tactic.
This one is scary in it’s precision. It was sent to only two email addresses. Both recipients have higher level network and financial access. The email looks like this
It looks innocent enough. In fact, if you check the link it goes to a Microsoft site. Clicking the link takes you here.

This is a legitimate OneNote notebook. The icons however are just pictures, not clickable links and the links below them are flagged as malicious. Had the user clicked on the link, their login credentials would have been quietly harvested.
In this type of attack, the hacker often shares or pretends to share a document with you. The email usually asks for your input and is purposely vague and low key. Should you open one of these documents and find only links to another document, close the document and contact the IT Service desk. Your quick action could save your data.
Chase Bank & Amazon phishing emails arriving in MRU inboxes – 09/26/19
A couple of extremely well done phishing emails that appears to come from Chase Bank and Amazon have appeared in Mount Royal inboxes. Interestingly enough, both come from the same email. Here is what they look like:


Criminals are getting better and better at creating emails that trick us into clicking. Remember, if you receive an email from an organization that you know, visit their website using a bookmark or search result and login to your account. You should be able to read any notifications from there. If not, you will be able to find official contact information so you can inquire about the legitimacy of the email that you received. If you find one of these nasty things in your inbox, delete it.
Fake email from Tim Rahilly arriving in spam folders – 09/18/19
This week the campus community is finding a particularly clever phishing email in their spam folders. It looks like this:

This is the third time our illustrious leader has been impersonated. Although this email is mostly landing in spam folders, I thought I should bring it to your attention in case it sneaks into an inbox or two.
Your on-the-ball colleague caught this one because they checked the sender’s email address. This is a gentle reminder to follow their lead. With all emails that ask you to take some sort of action, whether it is opening an attachment, clicking on a link or providing information, always check the sending email address BEFORE you read the email. If the email address is wrong, it is less likely your emotions will be triggered and rational thought will be by passed.
If this darling arrives in your spam folder or inbox, it can safely be deleted.
Clever Staples phishing email showing up in MRU inboxes – 09/05/19
Classes have begun and the hackers are betting that employees across campus will be ordering supplies. They have begun sending out fake order confirmations from Staples. These emails are extremely well done. Take a look.

I especially like the note at the bottom that specifically asks you to reply to the email. Just in case you are suspicious, they have given you some lovely directions that will put you in touch with them. Very clever.
The only real tell, unless you are super familiar with the email that Staples uses for order confirmations, is the View here button URL that takes you to chainetwork.club. Definitely not Staples.
As with all other emails that come from organizations that you are familiar with, visit their website directly to check orders, confirmations and payments. Do not use links in emails even if they look as legitimate as this one.
MRU employees receiving email requests over the phone – 08/23/19
This week several employees reported receiving calls from someone claiming to be from Adobe asking them if they wished to receive emailed documents about their products. Those who reported the calls declined, so I can’t say if the calls were legitimate sales calls from Adobe or if they were pretexting calls. Regardless of which they were, agreeing to be emailed documents usually doesn’t end well.
If the calls are legitimate sales calls, you could be agreeing to receiving hundreds of spam emails. If they are pretexting calls, the email they send you could have malware attached to it or contain a link to a webpage spoofing a legitimate site designed to steal your login credentials. To add to the misery, they could then take any information that you have given them over the phone and use it to create additional phishing emails that are almost impossible to detect.
Unfortunately this is the second time that we have had these type of calls on campus. As pretexting is on the rise, I suspect we are going to see a lot more of them in the coming months. This is a gentle reminder to be alert if someone calls you asking you for information they should already have or asks for personal information they shouldn’t know.
If it is a sales call and you are interested in their services, hang up the phone and call the company using a phone number listed on their official website. If it is from an organization that you know, hang up and call them directly using a phone number you know is legitimate. Never call them back on a phone number they give you.
MRU targeted by phone – 08/08/19
This week a rather irritating phone campaign has hit the campus. Phone solicitors are calling employees and asking them to confirm their role. If the employee does, the caller asks if they can send them some email. This particular campaign is more annoying than malicious. However, it provides a great opportunity to review phone safety.
With people becoming more tech savvy and cybersafety aware, it is becoming harder for criminals to score with a simple phishing email. To increase the odds that their potential victims will be tricked, they are turning more and more to pre-texting. The phone is fast becoming their favorite tool.
Typically a target receives a phone call with the scammer pretending to be someone who is trusted or has a right to the information they are asking for. They will often ask questions that seem innocent enough. However they are gathering information about you and the University that they can use against you later. Armed with enough information, they can create a phishing email that is almost impossible to identify as malicious.
If you receive a phone call from someone who is asking for information they should already have or that they shouldn’t know, politely ask them for the name of their organization and then tell them you will contact them later. You can then hangup and call that organization directly using a number that you have either used before or comes from the organization’s official website. If you cannot reach the individual through the organization’s switchboard, then you know that it is a scam.
Iranian hacker group using LinkedIn to deliver malware – 08/06/19
FireEye has identified a new phishing campaign targeting oil, gas and energy companies as well as utilities and government organizations. The rather clever criminal contacts victims through LinkedIn claiming to be a researcher at the University of Cambridge. Once contact is made, the victim is offered a job and asked to provide a resume. As part of the application process, they are also asked to go to cam-research-ac.com to download and fill out a document. Of course once they do, malware is loaded onto their computer.
What makes this campaign so concerning is the assumed legitimacy that comes with using LinkedIn to communicate with potential victims. People tend to trust the platform and therefore trust those that use it to communicate. Unfortunately, this trust is misplaced.
When you are contacted by someone you don’t know on any social media platform, treat that communication with the same skepticism as you do with any email message. Just because they say they are from a trusted organization, does not mean they are. Before you engage in conversation, call their organization and confirm that they are in fact employed there. A little homework can save a lot of headache.
Watch out for fake Equifax settlement emails – 08/01/19

Cybercriminals are sending out fake Equifax settlement emails. These emails are promising free credit monitoring and/or compensation. To make matters worse, they are spoofing the real Equifax settlement page. So if you click on the link in the email, you are sent to a very convincing web page encouraging you to file a claim. Of course, if you fill in their form with all of your personal information you are just sending your data to the criminals.
If you need to file a claim, do so by visiting the FTC website. You can find information there about the data breach and the settlement as well as a legitimate link to the Equifax site. Do not click on any links in any email that appears to come from Equifax. Visit their site directly using a browser search result or a bookmark. Everything that you need to know you should be able to find there. If not, there will be legitimate contact information you can safely use.
Fake benefits enrollment email arriving in MRU inboxes – 06/28/19
The following email is showing up in inboxes around campus.

This fake email is not from the IT Service Desk. Normally I would go through and show you all the things that are wrong with this email. However, as many of you have been readers for a while, I thought it would be nice to have some fun with this one.
Take a look at the email and then comment below on what you think flags this email as phishing. Next Thursday, I will go through the comments and add any that were missed. Let the commenting begin!
