Student Sponsorship dodges a gift card scam – 02/09/2024

Spoofing is when an attacker sends an email that appears to come from someone you know. We have seen this attack method used to target the MRU community before. This time, the target was Student Sponsorship and the attacker was spoofing a well known sponsor. Here is the original email they received.
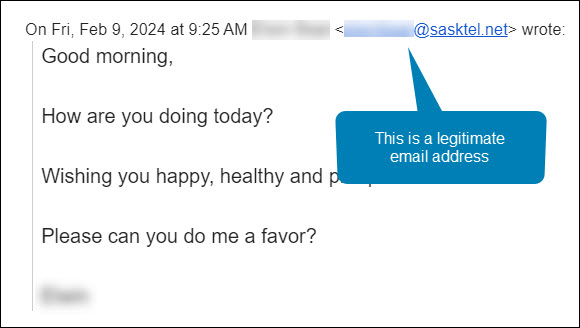
Maha was manning the Student Sponsorship inbox that morning. She was very familiar with both the sender’s name and email address. She hit the Reply button and asked the sponsor how she could help. Here is her response.
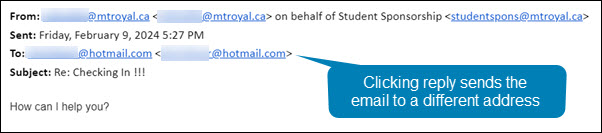
Notice how even though she hit reply, the email address in the To: field is no longer an @sasktel.net email address, but is now an @hotmail.com email address. This could only happen if the sender had edited the email header information so that the displayed sender email address was different than the replied to email address. In other words, they spoofed the legitimate email address.
There are legitimate reasons why this may be done. For example, a company wants to send with one email address to increase deliverability and a second one to receive emails because it is easier to remember. However, both emails will have the same domain name (the name that appears after the @). In this case, the second email address was created by a generic email provider. This is the reply that Maha got back.
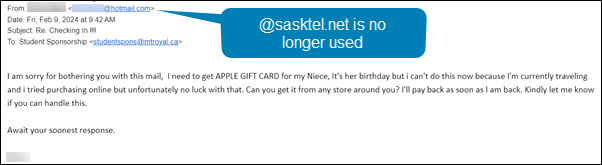
This confirmed her suspicions that something wasn’t quite right. The response she received back was no longer using the @sasktel.net email address and was asking her to make gift card purchases, it was a gift card scam. She forwarded the email to cybersecurity@mtroyal.ca immediately. Her quick actions saved her hundreds if not thousands of dollars.
When replying to emails, take a quick peek at the To: field. If the email address is different than the one that sent the email, proceed with caution. Someone may be trying to steal your money and/or your data.
New employees being targeted by the gift card scam – 11/02/2023

Universities are seeing another increase in gift card scams. However, this time they are targeting new employees. Those new to the University are unaware of policies and procedures around gift cards as well as the reporting structure. This makes them an easier target for criminals.
This is how the scam works. Attackers scan LinkedIn for those announcing they have started a new position at a university. Then they research the university and find the people most likely to be the new employee’s supervisor/chair/dean. They use this information to craft a very convincing email asking if the new employee is available.
Once the employee responds, they ask them to purchase gift cards for an employee reward program or some other plausible reason. The fake supervisor/chair/dean is usually in a “meeting” and only reachable by email. They add this detail to discourage the new employee from trying to reach the impersonator by other means.
If you are a new employee, be aware that no one at MRU will ask you to purchase gift cards with your own credit card. Suspicious emails that you receive can be reported by using the PhishAlarm button or by forwarding it to cybersecurity@mtroyal.ca
If you have a newer employee on your team, please let them know about this scam. Encourage them to contact their supervisor/chair/dean by phone or in person to confirm any requests to purchase gift cards. Your advice could save someone thousands of dollars.
Alert – Scammers user Flickr accounts in sextortion scam – 10/10/2023
Attackers are using compromised Flickr accounts to send email messages containing malicious links. The emails appear to list links to explicit images of the recipient. When they panic and click on the links to determine if the images are of them, malware is loaded onto their machine. The malware steals their login credentials.

If you receive an email demanding money and threatening to expose embarrasing or compromising images or information, report the email to IT Services using the PhishAlarm button. If the button is not available, you can report by forwarding the email to cybersecurity@mtroyal.ca. To remove the email from your inbox, report it to Google by clicking on the three dots in the upper right corner of the email and selecting Report phishing from the drop down menu.
Smishing attack thwarted by faculty member – 03/14/2023
It was just after 11:00 AM on a Friday when Kelly Sundberg received this text message
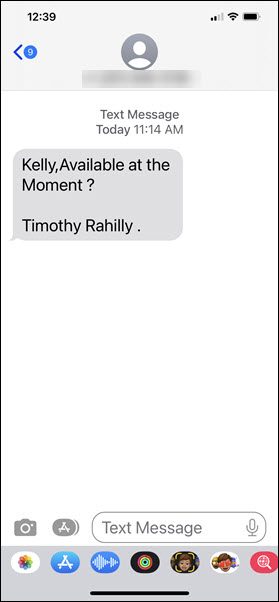
This was an odd request as the text was coming to Kelly’s personal phone. However, if something was urgent, maybe it was Tim texting him. What Kelly did next saved him from being scammed out of thousands of dollars, he contacted the Presiden’ts office and asked if it really was Tim that had texted him.
As it turns out, Tim wasn’t even in the city. The text had definitely not come from him. It had come from a scammer whose next move would have been to convince him to purchase gift cards as rewards for hard working colleagues.
Before you say, “I would never fall for that scam”, know that more than one person on campus has. It isn’t because they are stupid or because they didn’t take their cybersecurity awareness training. They became victims because the attackers are just that good at confusing you, creating urgency and getting you to react instead of think.
Kelly did two very important things right, firstly he stopped and let his rational thought kick in before he took action. As a result, the attackers did not have a chance to confuse or manipulate him. Secondly, he followed the guidelines in the cybersecurity awareness training, verify before you take action.
No matter how certain you are that a text or email is coming from your boss, if an unexpected request is made, call the sender and make sure the message actually came from them. That one step saved Kelly, it could save you too.
MRU community hit by tech support scam – 04/29/21
The tech support scam is back. This week a MRU community member had a virus warning popup on their screen while they were working. The virus warning listed a phone number and appeared to come from Microsoft.
The individual phoned the Service Desk. However, when they couldn’t get through they called the ‘Microsoft’ number in the pop up. The fake Microsoft rep hung up on them when the caller didn’t provide the rep with the information they were looking for. Our MRU community member avoided being scammed simply by not being cooperative. However, had they been dealing with a more patient scammer, this could have gone very wrong very quickly.
This is a reminder if you see a dialog box with a virus warning and a phone number, it is a scam. Most likely there is no virus on your machine. instead, the website that you have visited has been compromised by a hacker to display a fake virus warning to anyone who views it. If this happens to you, close your browser and then open it again. Do not close the pop up. Do not visit that website again.
If you are concerned that your MRU issued device may have a virus, contact the Service Desk. Be patient, they will get back to you. If it is your personal device you are concerned about, run a virus scan. If something appears to be amiss and the virus scan does not find anything, take your device to a repair shop to have it checked.
Coronavirus based attacks are rampant – 03/19/20
As employees all over the world are working from home, criminals are ramping things up hoping to take advantage of the less secure networks that people tend to have at home. We have surges in phishing emails on campus and across the world related to working from home as well as an increase in malicious websites. It has gotten so bad the US Secret Service has issued a warning. Here are some things to watch out for.
The fake VPN
As employees struggle to setup a home office, they are signing up and downloading VPN services at record rates. While all of our employees have the advantage of using SRAS, many smaller organizations do not have their own VPN tool and are asking employees to install one on their home computer. If your spouse or roommate are in this situation, warn them to be very careful about what VPN they download. Cyberattackers are offering fake VPN services that download malware onto your machine in record numbers. Make sure they check reviews of the service to ensure it is reputable before they install it on their machine.
Fake COVID-19 trackers
As people attempt to live their lives and stay safe, many are turning to maps that track the location and incidence of infections. Criminals are getting wise and creating their own versions of these tracking websites that infect your computer with malware.
Some enterprising scammers have also created phone apps that supposedly track the infection rate but load your device with ransomware instead. Stick to well known and reputable websites such as Alberta Health Services and the World Health Organization to get your information about the virus and stay away from any apps related to it including ones that tell you how to get rid of it.
Phishing emails about working from home and COVID-19
Phishing email attacks are off the scale. Everything from fake emails from your organization about working from home, to offers of vaccines and cures. One of their favorites is fake GoFundMe pages with coronavirus victims pleading for medical help. Another is pretending to be a colleague who is quarantined and needs help.
You name it, the depraved are going to try it. During this time it is especially important to be vigilant. If you receive an email that doesn’t come from a Mount Royal email address, question its validity. While you are working at home, make sure you use your Mount Royal email address to send business correspondence. DO NOT use your personal email address. This will make it easier for your colleagues to stay safe.
Sources:
https://www.securityweek.com/researchers-track-coronavirus-themed-cyberattacks
https://www.securityweek.com/other-virus-threat-surge-covid-themed-cyberattacks
How to prevent a two factor authentication compromise – 03/04/20
This week I posted an article telling the horrific tale of a Mount Royal employee who had their phone number ported to another carrier and their email compromised even though they had two factor authentication enabled on their email account.
How was this possible? The authentication method that they had used was an SMS message sent to their phone. With this method, who ever has control over the phone number receives the authentication codes. The bad news is, if someone impersonates you and either asks for a new SIM card or moves your number to a different carrier they can get access to your email account. The good news is, there is a way to stop this.
Instead of using a text message sent to your phone as your second step, use an authenticator app or authenticator key. An authenticator app generates an authentication code using wifi, while an authenticator key must be plugged in or waved near a device for you to login. In both cases you have to be in physical possession of the second factor to get access to your account. Of course if your phone is stolen or your key is lost, you are locked out. However you can print off backup codes and have an extra key available in case that happens.
Identity theft in 2020: Everyone is a target (a MRU employee tells their story) – 03/04/20
As coordinator of the cybersecurity awareness program here at MRU, I often have colleagues call me with their own personal tales of horror. One of the more recent ones involved a Port-out-scam. Here is a their tale, written in their own words…
Until recently, identity theft was definitely something that we never thought could happen to us. It’s something that we warned our grandparents, our parents and even our security-relaxed friends about. But we were totally safe, or so we thought.
Through this experience our lives have definitely changed forever. We have learned a great deal and are now more aware, and will be more vigilant. It was shocking to discover how easy it might be to lose everything.
Upon landing at the airport in Calgary at 2 AM following a holiday early in January, my boyfriend (for privacy we will call him James) turned his phone on to discover that he had no carrier service. We didn’t think it would be anything serious and joked about something being wrong with his last payment.
The next morning James called Telus and a Customer Service Agent informed him that he had ported his number out to Bell on Tuesday, to which he quickly replied that he had been out of the country, so that was impossible. After some convincing that this action was not taken by James, Telus quickly, and easily, ported the number back from Bell. We knew at this point that something was very wrong. He was also unable to get into his Microsoft Outlook email account; his password was denied.
Once James had his number back, he was able to use his phone (with SMS two-step authentication) to reset his password and get into his email accounts, where we quickly realized the horrifying truth that his identity was compromised. Someone had accessed his email account with his phone number, changed the password, and taken over. James’s email account is connected to everything: PayPal, Amazon, personal & joint banking, investments, taxes, etcetera. I am sure you can imagine the anxiety James and I felt in that moment of realization.
You’re probably thinking that James did something to be a target. He must have been lenient with his security questions, or displayed some weakness with online purchases or social media. We have gone over everything meticulously to try to figure this out, and with the help of many people, our conclusion is that he actually did nothing wrong. All the hackers needed to access his email was his phone number. He is not a prominent person and does not hold a prominent position, so not your typical target according to experts. Further, he is very private and careful, with the strongest security settings on his social media accounts where he is also conscious about everything he posts, and any business he does online shopping with.
Next came the long process of regaining control…. cancelling credit cards, bank accounts, informing all business and friends of the identity theft…setting up security watches on James’ Social Insurance Number through various government services…..hours of waiting on hold, explaining the situation and the frustrating experience of having to convince people of the seriousness of the situation.
We talked to Calgary Police Service (CPS), and while they made some good suggestions of things to change, credit checks to put in place, it was also frustrating that there was nothing they could do. Because no physical property was actually taken there will not be an investigation. We were also informed that we should maintain a close eye on all of James’ accounts for at least six to eight years as we don’t truly know what information the hackers obtained and they may resurface at a later date.
Microsoft Outlook support was useless because the same security measures that should help in this situation caused serious issues. The hackers were able to change the security settings in the account before James got it back. They added their own email addresses and phone numbers as new two-factor authentication security. It is part of the Microsoft Outlook security plan that when changes are made there is a 30-day freeze before further changes can occur. Despite hours speaking with Microsoft Outlook staff at all levels, they refused to close the accounts before the 30-day freeze.
Through all of this we learned that this is called a Port-out Scam. In this case, Telus confirmed to James that his account number was provided to Bell in the port. There was an incredible lack of due-diligence to verify one’s identity in this case. This type of scam has been known to play on the emotions of customer service agents at telecommunications companies and the lack of security measures in place to protect customers.
How does it work? The hacker would have acquired James’s name and phone number from somewhere to start – not difficult given the world we live in. Next they might have called Telus, pretending to be James, claiming they want to make a payment on their account, but they are not at home and didn’t have their account number – can they have it? The customer service agent should refuse, or ask detailed security questions only James can answer, but instead they provide the number. (CPS told us that hackers can also get addresses, email addresses and more this way) Next, armed with everything they need, they simply call another company (Bell in this case) and pretend to be James, saying they want to port their number over from Telus. Just like that the hacker owns your number and now they can get into anything your number is tied to for two-step authentication.
James called Bell to inform them of the theft and that they were used in the process of the theft, and, surprisingly, they brushed him off. Told him it was not their problem. Wanting to understand how this could possibly happen, I called Bell to casually inquire about moving over from my existing carrier and told the customer service agent I wanted to keep my phone number. She was more than happy to assure me it was no problem to keep my number – all I needed was my number, and to ensure my account with my previous carrier was in ‘good standing.’ It was way too easy.
The comical part in this experience is that while it was so easy for the hacker to steal James’s number, in order to cancel his phone number (once he got it back) the Telus Customer Service Agent’s protocol was to hang up and call James back to verify that it was his number, as well as asking for detailed account information and his driver’s licence number. This means that there is protocol that exists, but no assurance that it is followed regularly.
We are sharing this story as we hope that others will learn from this. We want telecommunications companies to start taking security seriously and we want you to be vigilant. Instead of assuming you are taking precautions and you are safe from identity theft, in 2020 it is safer to assume you are a target and take precautions for the day you will be attacked.
Mystery Blogger
(MRU Employee)
Is there a way to use 2FA that will provide security even if you are a victim of a port-out or SiM swap scam? Yes there is. Read How to prevent a two factor authentication compromise to find out.
Beware of tutors posing as MRU professors – 01/28/20
One of our students gets the cybersecurity hero of the month award. This very sharp and vigilant student posted a Kijiji ad looking for a tutor. He received a response from a gentleman claiming he was a professor at Mount Royal University. Rather than take the man at his word, the student wisely made inquires first with his department chair and then with others. No one could vouch for his employment past or present.
Bravo to this smart young man for checking the perspective tutor’s credentials! Because he took the time to check for references and confirm that the person is who they said they were, he avoided paying a premium price for a not so premium tutor.
Well done!
SIN number scammers calling MRU employees – 10/25/19
Mount Royal employees are receiving fraudulent calls from individuals pretending to be from the Canadian government. The caller explains there is an issue with your SIN number and as a result you are subject to legal action. You are asked to contact them immediately. Upon contacting them, you are told you must pay thousands in bitcoin to avoid being charged with fraud. This scam is similar to one currently making the rounds in Regina.
What makes this scam so concerning is the fraudsters are spoofing government agencies so the call looks like it is official. As well they are often robocalls which makes them sound even more legitimate. In response, the Canadian Anti-Fraud Centre has issued an alert asking people to be vigilant.
No government of Canada agency will call you over the phone and threaten you or ask for payment. Neither will the RCMP or police. If you receive a call of this nature, hang up the phone. If you are concerned there may be an issue with your SIN you can contact the government directly by visiting their website. You can also check with Equifax and Transunion to see if your SIN has been used to obtain additional credit without your knowledge.
